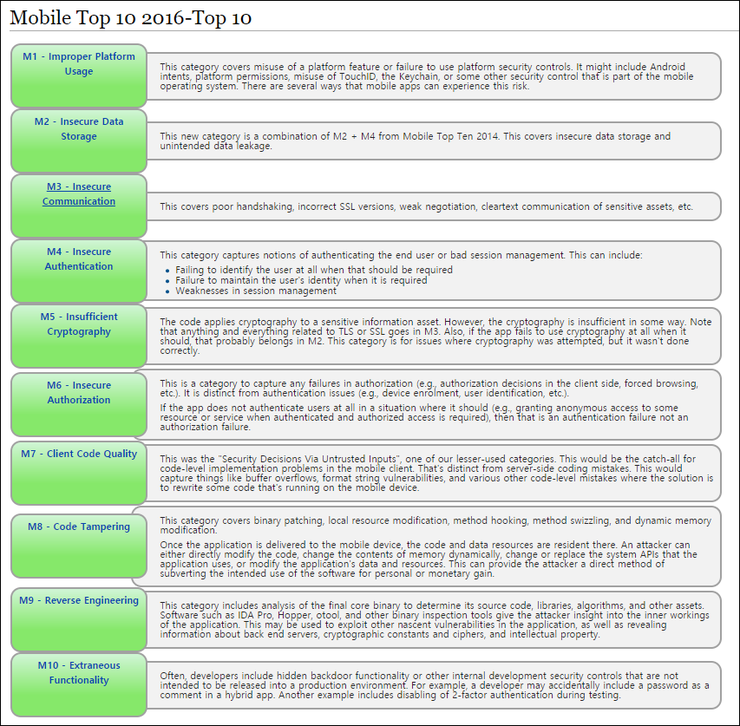
They are ordered by order of importance with control number 1 being the most important. OWASP Top 10 Mobile Security Risks - 2016.
2016 Owasp Mobile Security Risks Top 10 네이버 블로그
A proof of concept video follows this article.
. OWASP TOP 10. Top 10 Raw moments. Cross-site Scripting XSS 4.
M1 Improper Platform. We formalized the OWASP Top 10 data collection process at the Open Security Summit in 2017. The OWASP Top 10 is a regularly-updated report outlining security concerns for web application security focusing on the 10 most critical risks.
Adopting the OWASP Top 10 is perhaps the most effective first step towards changing your software development culture focused on producing secure code. OWASP TOP 10. Read what they are and what we can expect for the future of mobile security.
Several high-profile cases have highlighted the ease with which hackers can target mobile applications and the lax security practices at some of the worlds largest organisations. Read full article OWASP TOP 10. OWASP TOP 10.
M3 Insecure Communication不安全的通信 This covers poor handshaking incorrect SSL versions weak negotiation cleartext communication of sensitive assets etc. Verify for Security Early and Often 2. Its now grouped together with identification failures in a new category called Identification and Authentication Failures in the.
Top 10 Raw moments. OWASP Mobile Top 10 2016. Check your Website Security Issues with Indusfaces Free Website Security Scan.
This covers insecure data storage and unintended data leakage. Security feedback during code review is your opportunity to learn feel more engaged. OWASP Mobile Top 10 2016.
Insecure Direct Object Reference. This corresponds to the OWASP Top Ten A3 - XSS Category with a technical impact of moderate. Insecure Direct Object Reference allows attackers to manipulate references to gain access to unauthorized data.
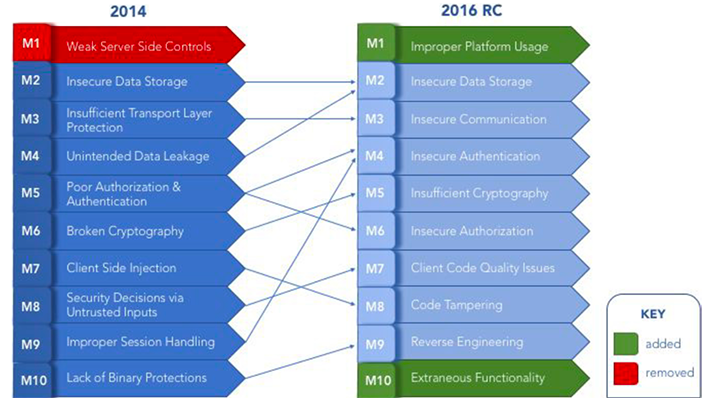
Updated every three to four years the latest OWASP vulnerabilities list was released in 2017. The 2021 edition is the second time we have used this methodology. WWE Top 10 July 18 2016 - YouTube OWASP Top 10 Proactive Controls 2016 10 Critical Security Areas That Web Developers Must Be Aware Of About OWASP The Open Web Application Security Project OWASP is a 501c3 non for profit educational charity dedicated to enabling organizations to design develop acquire operate and.
WWE Top 10 July 18 2016 - YouTube OWASP Top 10 Proactive Controls 2016 10 Critical Security Areas That Web Developers Must Be Aware Of About OWASP The Open Web Application Security Project OWASP is a 501c3 non for profit educational charity dedicated to enabling organizations to design develop acquire operate and. If you havent already please check out our OWASP Mobile Top 10 2016. Application Business Specific.
Top 10 Mobile Risks - Final List 2016. The OWASP Top 10 is the reference standard for the most critical web application security risks. Ad Mitigate OWASP Top 10 vulnerabilities and Improve Website Application Security.
Cross-site request forgery XSRF 9. OWASP has released the 2016 OWASP Mobile Top 10 Vulnerabilities report. Parameter Manipulation insecure direct object reference 5.
OWASP Top 10 is the list of the 10 most common application vulnerabilities. M1 Improper Platform Usage. Broken Authentication has moved down the list to position 7 because it seems to be less of an issue due to increasing adoption of standardized frameworks.
Insecure Deserialization allows attackers to transfer a payload using serialized objects. This is the second article in our OWASP Mobile Top 10 series which aims to flesh-out the OWASP recommendations with some concrete examples that you can apply to your iOS and Android applications today. This new category is a combination of M2 M4 from Mobile Top Ten 2014.
OWASP refers to the Top 10 as an awareness document and they recommend that all companies incorporate the report into their processes in order to minimize. The business impact of this vulnerability corresponds to the business impact of the associated vulnerability defined in the OWASP Top Ten that the adversary is exploiting via the mobile device. The OWASP Top Ten Proactive Controls 2016 is a list of security concepts that should be included in every software development project.
A great deal of feedback was received during the creation of the OWASP Top 10 - 2017 more than for any other equivalent OWASP effort. Ad Your code is more secure with SonarQube to automatically detect OWASP vulnerabilities. OWASP is a non-profit organization with the goal of improving the security of software and the internet.
This shows how much passion the community has for the OWASP Top 10 and thus how critical it is for OWASP to get the Top 10 right for the majority of use cases. OWASP Top 10 leaders and the community spent two days working out formalizing a transparent data collection process. This happens when integrity checks are not in place and deserialized data is not sanitized or validated.
Modern connected mobile applications are coming under increased pressure from hackers and malware on both iOS and Android. OWASP TOP 10. The report is put together by a team of security experts from all over the world.
Through the project our goal is to classify mobile security risks and provide developmental controls to reduce their. It also shows their risks impacts and countermeasures. Using Components with Known Vulnerabilities.
The OWASP Mobile Security Project is a centralized resource intended to give developers and security teams the resources they need to build and maintain secure mobile applications. M2 Insecure Data Storage.
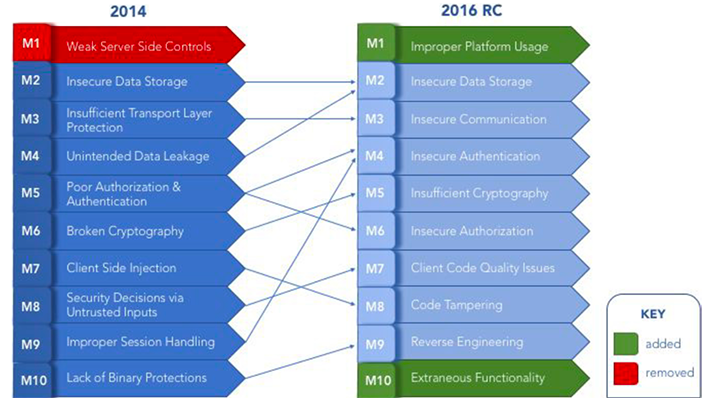
2016 Owasp Mobile Top 10 Risks Vs Owasp Mobile 2014 Rc
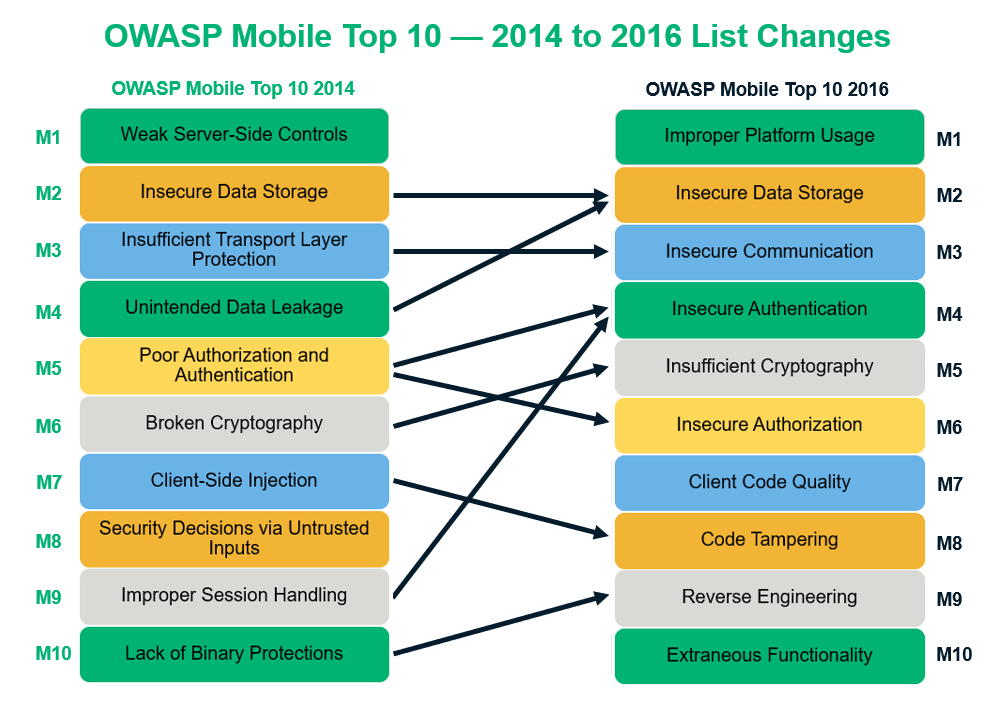
Owasp Mobile Top 10 Vulnerabilities Mitigation Strategies Infosec Insights

0 Comments